Key Takeaways
- Risk-based testing (RBT) prioritises your test suite by the likelihood and impact of failure, so your team spends time where it matters most.
- Risk assessment is a core part of the process, not a one-time setup. Your team revisits and updates priorities throughout the project lifecycle.
- RBT works across industries and scales well in Agile, CI/CD, and regulated environments where testing resources are always limited.
- The process covers seven stages: product analysis, risk identification, risk analysis, test planning, test execution, review, and ongoing monitoring.
- RBT fits best when resources are tight, projects are complex, or the cost of a missed defect is high.
Here is what risk-based software testing looks like in practice and how to avoid the mistakes that make it fail. 👇
Definition of risk-based testing
Risk based testing in software testing is the practice of prioritising your QA efforts based on the likelihood and impact of failure, so your team focuses on what actually threatens the product. In many cases, software complexity rises exponentially, so just hiring more testers is not a solution anyway. Instead, defining the right scope of testing becomes crucial to ensure that high-risk areas get the most attention.
In this context, risk can be defined as the odds that an undetected (=unresolved) bug negatively affects the software. In reality, understanding risk-based testing is a little more complicated, as not every bug has the same negative impact. A text stretching past the text box may be a frequent issue in the German version of your software but may cause little functional trouble. On the other hand, rare instances of duplicate payment will always be a major headache, especially when payment providers keep the flat transaction fee even after a refund.
Key risk-based testing features
Risk-based testing has a number of key characteristics that set it apart from traditional testing:
- Test what matters, don’t test everything is the main principle of risk-based testing. Traditional testing always has edge cases that happen so rarely that even testers may not always think of them. RBT takes this a step further: even when you already have the test cases, don’t dwell on executing them all when you don’t have the time.
- Risk assessment becomes a major part of QA when using RBT. Risks with low odds but high impact demand more resources than high-frequency, low-impact problems. This sounds hard in theory, but there are practical ways to categorise risks that we will cover later in the article.
- Synergy with company-wide risk management policy extends the value of risk-based testing beyond software development and testing. Banks make a good chunk of money on transaction fees, so transactions not happening is a critical risk. Consequently, a failure in 3DS verification for online payments is a critical risk for the bank’s web application.
Benefits of risk-based testing
Risk based software testing delivers value beyond just finding bugs faster. It changes how your team allocates time, justifies decisions, and builds confidence in every release.
- Resource utilisation is the core reason for applying risk-based testing. Realistically, your QA planning is about how many hours the team has, not how many features and code additions they need to validate. Testing only components that are the most likely or painful to fail is a great way to maximise the value of your testers.
- Automation optimisation is a major benefit, too. It may seem that test automation circumvents the man-hours limitations, but somebody still needs to write, maintain, and keep up with automated tests. There are also server costs that make 100% 24/7 test automation unfeasible for SMBs and often even large companies. The knowledge of what to target with scripts will be a great companion to a list of priorities from manual testing.
- A demonstrable increase in software quality is great for both user and stakeholder confidence in the product. Risk-based approach in testing is not just about reducing resources on trivial issues — it also means spending more time on what matters. If a user sees that an app stopped crashing every few hours, they will note an improvement. If you use RBT to release an app that never crashes, you will provide more value compared to fixing cosmetic defects.
- Early issue detection is great in general, but it works even better when applying risk-based testing in Agile teams. Testing critical components first means that you are likely to discover significant issues early. This allows everyone on the team to adjust their schedules and prioritise making these components work alongside the most significant additions from the new build. Alternatively, the devs would have proceeded to work on nice-to-have features and would not have had the time for bug fixes.
- Simplified regulatory compliance is a major benefit for any company working in a sensitive industry. Regulators often expect you to have sound reasoning behind your approach to software testing. RBT (=testing for risks) is a very reasonable and strategic approach to software testing that will keep you out of trouble in case something does fail.
When to use the risk-based testing approach?
Risk-based testing fits most naturally when the cost of missing a defect outweighs the cost of the extra testing effort. These are the situations where your team will feel the benefit most directly. It may seem like these situations basically cover every software testing type in existence. This is true to an extent: you are not obligated to RBT, but most teams face negative factors that this approach mitigates well.
- Limited resources are a problem anywhere but in startups, but only because they often don’t have any dedicated QA. If you don’t have the time to run and maintain all tests to follow up on your high test coverage, risk-based testing solves that.
- Complex projects mean that manual regression testing will take too much time to check for other issues as well. While test automation can largely reduce the burden, risk-based testing is a great way to cut down on repeatedly testing for the same minor issues.
- Mission-critical applications can’t afford to fail, and risk-based testing is arguably the best way to allocate more resources to critical issues. You will also have a factual justification to share with internal stakeholders and regulators.
- Legacy systems are by design too much to properly cover with tests. You are likely to face not only poor optimisation but a lack of documentation and compatibility issues as well. Focusing on the components that matter the most will make integrating and maintaining a legacy solution both easier and more efficient.
- Time pressure may be the biggest factor for relying on risk-based testing metrics to go over the finish line. Some product niches surface so fast it may be too late if you go through the proper QA cycle. Then there are investor milestones like getting something that works well enough before a Seed investment negotiation. Whenever you have to work faster than anticipated, RBT is the way to minimise the negative impact.
Who performs risk-based testing?
The same specialists who run traditional testing also carry out risk-based testing, but their responsibilities shift. Risk assessment and prioritisation become part of the job, not a separate process handled elsewhere.
QA specialists perform the majority of risk-based testing. They prioritise risks, create and maintain tests to safeguard against these risks, then execute tests and file bug reports to developers. Much like with traditional testing, developers and non-tech stakeholders are involved to improve collaboration and stay consistent with business goals.
Developers are nowadays expected to write and run unit tests. These tests cover short code snippets to spot basic errors. These errors are then promptly fixed by the developer. Code is sent to the QA only after unit tests stop returning errors. This fits risk-based testing really well, as QA specialists get more time to focus on complex issues.
End-users performing user acceptance testing are technically part of risk-based testing too. They run through the most likely use cases and spot issues so that they don’t ruin the experience when the software is signed off.
What are the types of risks during the software development process?
Risks in software development are usually categorised by their area of impact. The main types include:
- Functional risks pose a direct threat to the software’s (and potentially the company’s) operations. Individual components and the entire software can work incorrectly or outright breakdown. Risks associated with critical functionality or the app’s complete failure have the highest impact.
- Technical risks refer to the infrastructure risks for your software. Even Amazon Web Services technically may crash, let alone cheaper Cloud solutions. Tech debt may one day start a major spike in churn rate and ruin not only your app but your business model as well.
- Security risks are associated with negligence toward protecting your solution. Data leaks are a prime example, as breaches both stain a company’s reputation and result in financial loss. Fines are getting more and more costly, especially in the EU.
- Performance risks reflect potential service degradation for both existing users and potential customers. Your solution should be ready for peak usage hours and not crumble under a wave of new signups. Poor usability testing can also lead to frustrating user experiences, increasing churn and damaging your product’s reputation.
- Process risks cover potential problems that you face when working on the product. A new testing or development methodology may decrease or worsen the output, both short-term and long-term. A new release may go wrong, making you scramble for a rollback. Simply failing to meet a development schedule may also be a process risk.
- Business risks are introduced by the market reality that the company operates in. The product may go out of fashion or fall behind very fast. Regulators may come down on you for failing to meet the latest requirements. A software failure will cast a shadow over the entire company, even if it is just one isolated unit bearing the same name.
Dealing with these risks during the software development process requires a strategic approach to testing. For this, you need a Test Management System (TMS) that helps you with your risk management and streamlines your whole testing efforts. And what could be even better than a comprehensive Test Management System nowadays? Of course, an AI-powered one.
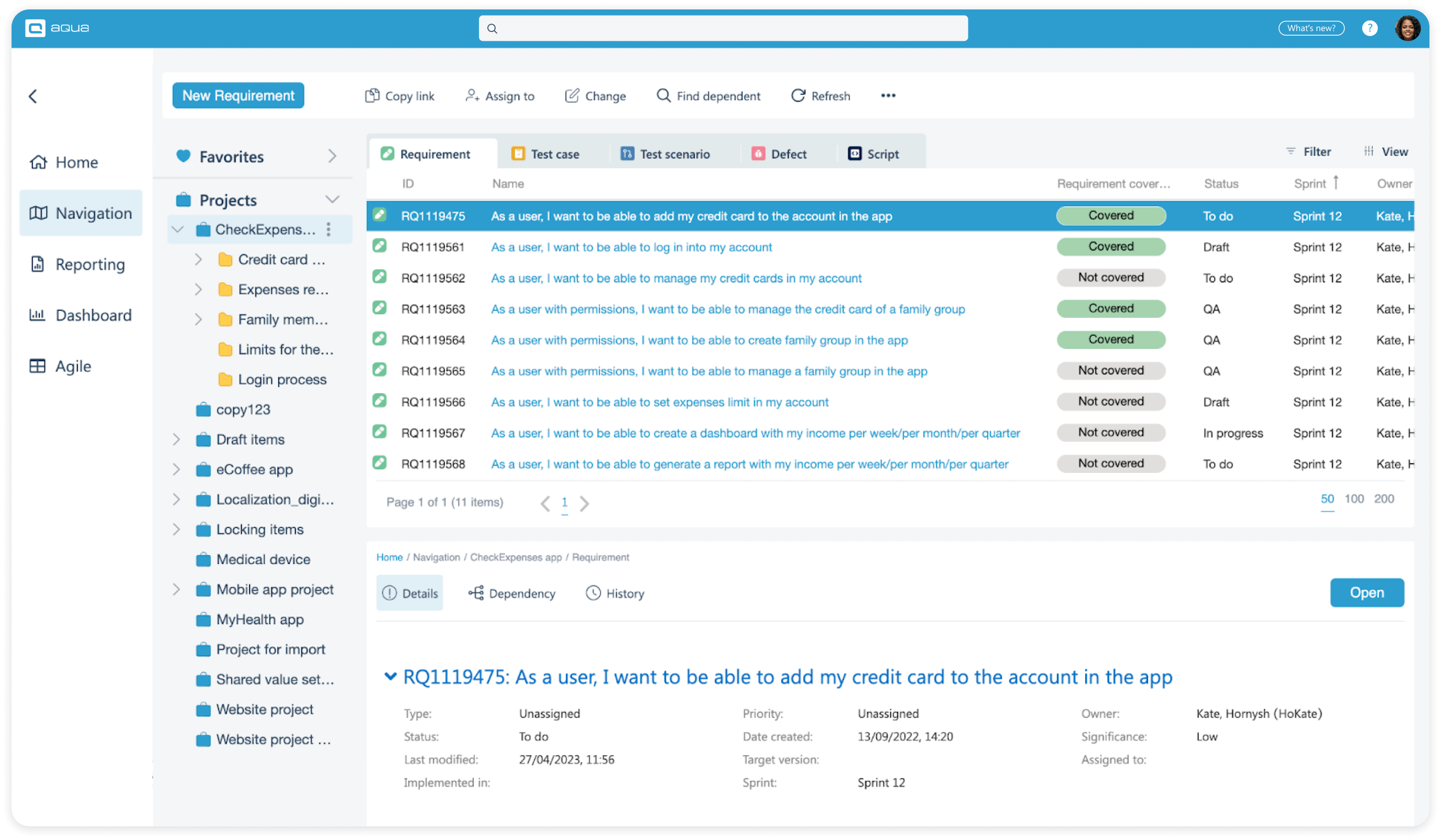
Imagine having a TMS that helps you generate requirements, test cases and test data within just 3 clicks. This will save up to 98% of your time and help you focus on where the risks are high. There is no chaos here that can cost you time and money: you have 100% traceability and visibility into your QA process, and everything can be tracked back. With aqua’s AI-Copilot you also get insights into what bothers you in the testing process. Other than this, aqua provides you with a centralised dashboard that will keep everyone in the team on the same page. Ready to bring German quality and precision into your testing efforts?
Save up to 98% of your time to focus on high-risk areas
How to define and determine risks in software testing?
Risk evaluation is usually carried out early in the risk-based testing. The process involves past data and input from all parties. Company-wide risk management strategy can be a great source of inspiration, as you know which events are the most crucial to mitigate.
Stages of risk-based testing
-
1
Product analysis is the earliest part of setting up risk-based testing. Tech people need to identify key functionality and study the project infrastructure. It is also important to consider external factors like business environment, regulator requirements, and non-tech limitations of the project
-
2
Risk identification is when stakeholders, devs, and testers come together to discuss potential risks. They use their knowledge of the project, historical information for similar projects, and industry expertise to identify potential issues. Generally, you would like to use creativity-friendly methods like brainstorming. The goal of this stage is to come up with risks, not immediately agree or dismiss what others came up with
-
3
Risk analysis is the most crucial stage. As risk-based testing uses the principle of 100% focus on highest risks, you need to define them properly. This includes assessing the likelihood and impact of individual risks. Once you have both, calculate risk exposure by multiplying the values. This result will be your primary way to rank risks to cover in testing
-
4
Test planning stage in risk-based testing is similar to traditional QA. You still need to create a testing strategy, but it should include the risks that you identified and prioritised. In early cycles, you would usually move fast and create tests for high-priority risks. This is especially relevant if you’re introducing risk-based testing to an existing project — there are plenty of existing tests that cover smaller things
-
5
Test execution is where you execute test cases, file bug reports, and work with developers to fix issues. While doing that, you may identify risk patterns that should be addressed by mitigation measured at team-wide, project-wide, or even company-wide scale
-
6
Test execution is crucial to be a dedicated stage on your timeline. This is where all stakeholders come together once again to discuss how the testing cycle went. The validity of risk prioritisation, discovered patterns, potential mitigation measured, and other improvement suggestions are all discussed. Key stakeholders then make action items for every party
-
7
Monitoring & adjustment makes you continuously watch the amended testing strategy play out and make corrections if needed. You add new test cases, update or remove less relevant tests, and also add new risks and prioritise them relative to initial risks
Examples of risk-based testing
To better illustrate the outcome, here are a few examples of risks that companies from several industries could identify:
Banking RBT example
- High-priority risks: transactions failure, incorrect transactions fee, currency exchange algorithm malfunction
- Medium-priority risks: lifestyle functionality failure, delayed transaction notifications, malfunctioning spendings dashboards
- Low-priority risks: typos, rare app crashes that do not affect transactions, temporary inability to access transaction history for 1+ year
E-commerce RBT example
- High-priority risks: items can’t be added to the cart, pricing errors, shipping calculation faults, checkout errors, fraudulent payment
- Medium-priority risks: UI failures, website outage during high-demand exclusive releases, faults with algorithm to block sales above available volume
- Low-priority risks: minor filters malfunction, slightly abnormal load times when displaying 100 goods
Automotive RBT example
- High-priority risks: failure of hardware-software car functionality, zero-day software vulnerability, circumvention of subscription requirements for car features
- Medium risks: failure to connect with a phone, media playback errors:
- Minor risks: poor fonts in translation for individual markets, convoluted menu navigation
Metrics of risk-based testing
The metrics for risk-based testing overlap with traditional testing, but there are a few unique metrics that you should consider as well.
- Severe & critical risks share
- Risk missed during testing (by severity)
- Risk missed to risks identified (proportion)
- Test coverage by app area (should be bigger for high risk)
- Defect density by app area (to validate risk assessment)
Best risk-based testing techniques
Since the actual testing is quite similar, risk-based testing techniques mostly concern the preliminary work on the project’s risks. Find some techniques below.
Risk identification techniques
Brainstorms are arguably the most suitable way to identify risks. Every stakeholder voices their opinion freely without the fear of nominating too many issues.
Additional risk identification techniques mostly rely on past data to help you with extra ideas. Checklists with risks for similar projects are an immediate source of inspiration. Historical data could be useful too, especially if this is a similar project and/or you are working with the same engineering team(s).
Risk analysis techniques
Risk matrix is the visualised version of how you ranked risks. There are several approaches, but a very common one is colour coding. Softer colours (e.g. green or yellow) denote less frequent and less impactful risks. Harsher colors (e.g. brown or red) point to high-frequency, high-impact risks.
Similarly, Failure Mode and Effects Analysis (FMEA) dwells on pessimistic scenarios and suits mission-critical software really well. You can also hold a rigid brainstorming session based on Structured What if Technique (SWIFT) to grade risks in sensitive industries faster than you could with FMEA.
Risk mitigation techniques
Automated testing for known risks is the most prominent risk mitigation technique. The more you can automate, the more time you have to cover lower-priority risks. You can also use that time for exploratory testing that will potentially reveal more risks in a very practical manner.
Risk monitoring techniques
KPIs are the best solution to monitor risks. If you see that any QA metric is abnormal, then you should look at either your test suite, your testing strategy, or your risk assessment.
The modern way to handle KPIs is to set up KPI Alerts. This functionality will automatically notify when there is an anomaly in your metrics. This feature is offered in aqua, a 100% traceability AI-powered test management solution for any scale.
Get KPI alerts for robust risk monitoring
How to use risk-based techniques to prioritise test cases and plans?
All these techniques will result in better-assessed risks. Here is how you could use that as part of risk-based testing:
- Create tests for areas identified during risk assessment first
- Prioritise test execution by risk level
- Use test automation to further reduce manual effort spent on lower-risk areas
- Use AI-ready test management solutions (aqua can help here) to create tests for edge cases
- Apply analytics to reallocate resources as you see critical areas fail more or less often
Mistakes to avoid in risk-based testing
While risk-based testing sounds exciting, doing it the wrong way will lower the QA output and at times even introduce more issues.
- Rushing through risk identification will make the picture incomplete. Even if you manage to assess and mitigate all other risks, issues of varying severity will pop up later. Make sure to allocate ample time and wait for stakeholders if unavailable
- Neglecting low-priority risks means a compounding debt that will eventually backfire. It could also be an increasing sort of frustration for both developers and end-users. While you can’t fix everything, keep low-priority risks on your radar
- Static risk management means that risk-based testing is only good for a few months if not weeks. You need to keep prioritising, analysing, and adding new risks as identified by business people, project stakeholders, and engineering teams
- Inadequate resource allocation may negate the gains of risk-based testing or even bring more trouble. If you are not aggressive enough, you are still wasting too much time on lower-priority risks. If you are too enthusiastic, some medium-priority risks ruin your day. Analysis and experience are the answers.
Best risk-based testing tools
In this section, we will look at test management solutions that are good fits for risk-based testing. While you may separately employ a risk tracker, the findings will still need to be used with a TMS to mitigate the risks.
- aqua is the most feature-rich and risk-conscious tool on the list. Regulatory compliance is proven by dozens of government, insurance, and banking clients. AI test generation to cover edge cases is the most advanced solution on the market. The tool comes with a neat test coverage section on the Requirements screen, showing whether a requirement is covered and offering previews for tests that cover the requirement. KPI Alerts are automatically issued as well.
- The Jira plugin for QA Xray alongside yet another Jira plugin called Risk Management can work together. Alas, Xray has extremely lacking analytics, lags behind competitors in advanced QA functionality, and no longer accepts clients that run Jira On-Premise (Atlassian sunsets it in January 2024).
- Kualitee is a decent option for risk-based testing due to decent dashboards and solid QA functionality. Alas, it has subpar suite of native integrations, does not offer KPI Alerts, and lacks workspace-wide logging for 100% traceability.
Keep your risk documentation accurate and up to date without the manual effort.
How to Create a Risk Scoring Model for Test Prioritization
A risk scoring model gives your team a consistent, repeatable way to decide what to test first. Without one, prioritisation relies on gut feeling and whoever speaks loudest in the planning meeting.
The standard approach uses two dimensions: likelihood and impact. Score each on a simple 1–3 or 1–5 scale, then multiply them to get a risk exposure score.
Step 1: Define your scale.
Agree on what each score means before your team starts rating. For likelihood: 1 means rarely occurs, 3 means happens regularly. For impact: 1 means cosmetic issue, 3 means critical functionality fails or data is affected.
Step 2: List your risk candidates.
Pull from your risk identification sessions. Include functional, technical, security, and performance risks. Keep each item specific enough to score, such as “payment gateway timeout under high load,” not “payment issues.”
Step 3: Score each risk as a team.
Do this collaboratively. A developer, a tester, and a business stakeholder will each bring a different perspective. Differences in scoring are a signal worth discussing, not averaging away.
Step 4: Calculate risk exposure.
Multiply likelihood by impact. A score of 9 on a 3×3 scale is your highest priority. Scores of 6 sit in the medium band. Scores of 1–2 go to the bottom of the queue.
Step 5: Map scores to test coverage.
High-exposure risks get full test coverage, automated regression, and priority in every sprint. Medium-exposure risks get coverage but can be reviewed less frequently. Low-exposure risks are documented and monitored, not necessarily tested every cycle.
Review scores at the start of each release cycle. Risks evolve as the product changes, and a low-priority item from three months ago may now sit at the top of the list.
How to Document and Report Risk-Based Testing Results
Good documentation turns your risk-based testing effort into something your whole team and stakeholders can act on. Poor documentation means the same risks get rediscovered next release.
What to capture during testing: For each risk in scope, record the risk ID, description, exposure score, test cases linked to it, execution status, and any defects found. Keep it in one place, not scattered across spreadsheets and chat threads.
How to structure the report: A concise risk-based test report covers four things. First, which risks were in scope for this cycle. Second, what the test results showed for each. Third, which risks were resolved, which remain open, and which were newly identified. Fourth, any changes to priority scores and the reasoning behind them.
Who the report is for: Your engineering team needs defect details and failed test references. Business stakeholders and regulators need a summary: coverage percentage, open critical risks, and sign-off status. Write both into the same document in separate sections.
When to update it: After each test execution cycle, not just at the end of the project. A report that only appears at release time gives your team no opportunity to course-correct during development.
A tool like aqua cloud makes this straightforward. Every risk, test case, and defect is linked automatically, so your report reflects the current state of the project without manual consolidation.
Risk management using risk based testing
Implementing risk-based testing shifts the paradigm from testing for finding the most defects found during testing to finding defects that matter the most. Setting it up will require a collective effort from the engineering team, non-tech stakeholders, business people, and possibly the entire team. As a result, however, you will get objectively better testing done with the same resources and elevate the quality of your software.
In conclusion, you need a robust testing solution to manage these risks effectively. A modern TMS will help you prioritise your efforts on what matters most, and make sure you don’t lose time on repetitive tasks. That is where you need aqua cloud, designed specifically for one purpose: taking away the pain of testing.
With aqua cloud, you can get:
- AI-Powered Insights: Use AI-driven capabilities to identify and address risks, and tackle the critical issues before they escalate.
- Comprehensive Coverage: Test all aspects of your software thoroughly, from functional and technical risks to performance and process-related concerns.
- KPI Alerts: Stay informed with real-time alerts for key performance indicators, and respond to issues quickly.
- Customisable Reporting: Generate customised reports to gain deeper insights into your testing processes, helping you make data-driven decisions.
- Robust Automation Integrations: Streamline your testing efforts with automation, providing quicker feedback loops and reducing the chances of oversight.
- 100% Traceability: Maintain complete visibility into your testing processes, ensuring that all risks are tracked and managed effectively.
Mitigate your risks with 100% efficiency with a modern TMS